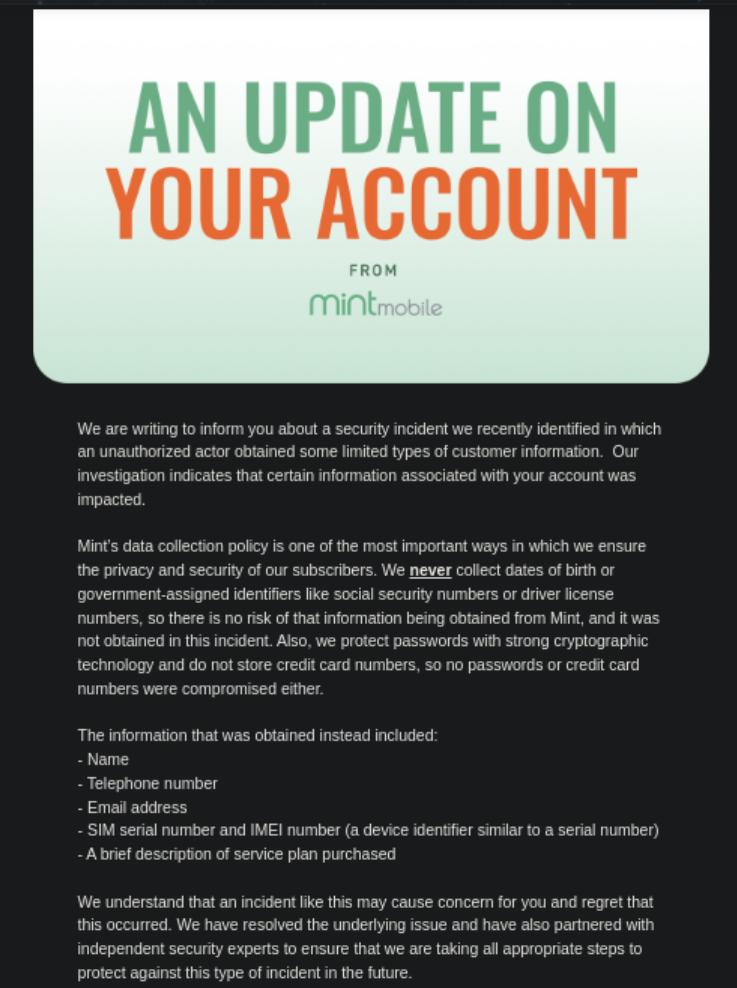
Every time that there is a leak like this it’s infinitely aggravating how the spin department tries to downplay what happened. If you are using SMS based MFA you probably want to stop doing that now.
Edit: sorry, app didn’t show the entire image by default, they DO list exactly what was lost, not a bad email tbh (although better if they didn’t lose it)
Isn’t it saying that they didn’t have those bits so couldn’t loose them?
It would have been more useful (but look worse for them!) If they just listed what was lost…
Isn’t the bulleted list the stuff that was lost? They say “we don’t have govt id stuff so that can’t be stolen, the CC info wasn’t affected, here’s the info that was potentially hit”
This seems like a great email to get. They know what subsystem was hit and are telling people.
I don’t think people understand the impact of IMEI and SIM serial being compromised. I’m not sure I fully do, either. This feels like when a mechanic gives you too much technical information that you don’t know how to process.
I definitely don’t either, but I sense that the email itself is supposed to be the infuriating part here. The scenario is mildly infuriating for sure, but the email itself is still about as good as you can get in my opinion. Quick, clear about what could be hit.
I was also wondering this. How often is this information available to apps/websites?
Mint is a mobile carrier so they have this information about your phone.
But is this something only carriers would normally have access to?
I thought it was a nice tidy list too.
How is it so hard for people to read?
People really, really hate clicking past the post, even if it’s just to a screenshot.
Heaven forbid its an article
My bad, app wasn’t showing the entire image. I need to try the other apps.
To clarify for people wondering, SIM and IMEI information is how the system knows your phone is… your phone.
Cloning it is supposed to be hard, but with it, they can receive 2FA messages like “Is This You? Text Y back!”.
It’s actually super easy, if they have enough information, to convince a carrier’s customer service that they are you (remember… never work the system when you can work the people who manage it.)
Yup and that’s the infuriating part. It’s not helpful or useful, it 100% a cya.
Your title implies they lost all the bad stuff though
With the IMEI and SIM card information they now have the details needed to take over MFA. I share my birthdate with people that I casually know, I try not to do that with MFA codes. Credit card details would be bad, but at this point with the number of people who have leaked it, I would be 100% surprised if you couldn’t find our CC data via a google search.
Setup TOTP NOW. Mint added proper TOTP authentication as MFA a while back that should block sms based MFA. Might be a good way to prevent sim swapping attacks.
Might work for mint but what about all the other accounts with other companies using mfa?
The goal here is to prevent someone from requesting a SIM replacement to unlock your other accounts. Since the attacker can use the IMEI and SIM info to contact customer service. If you have MFA on your mint account then they should ask for extra info before sending the replacement SIM, which would help with the current situation.
The reality is they may not know exactly what was obtained, but they do know it wasn’t anything they don’t collect (like DOB, SSN, etc listed in the message). Instead of looking at this purely as a CYA message, instead looking at it as informing you as soon as they had any idea your information may have been impacted instead of waiting weeks/months to inform you. Don’t let perfect be the enemy of good.
Don’t let perfect be the enemy of good.
This is nice. I’ma keep it.
Not seeing anything in my email about this one. Is it a new one or from earlier this year?
This is fresh… came in early this morning. Not sure if they got all of them or a subset.
But with name, email, phone number, and sim card serial number, it’s trivial for a scammer to do a sim swap attack …
They should replace the SIM card to all users immediately, at their expense
I think leaks should come with stiff penalty. Like the CTO goes to jail, pays each person involved for a lifetime worth of damage, and then has their head and arms locked in an old timey wooden head and hands stock lock at the center of town square where the public gets to throw rotten food at their face. No but seriously, they need to pay people affected a lot of money for potentially fucking their credit up because that’s where this kind of data goes.
Your username is alarming
Don’t you mean intriguing?
It can be both
They do know that that’s exactly the information that’s behind every scam right?